How to Configure Site-to-Site VPN Between WatchGuard Firebox T80 and Azure VPN Gateway
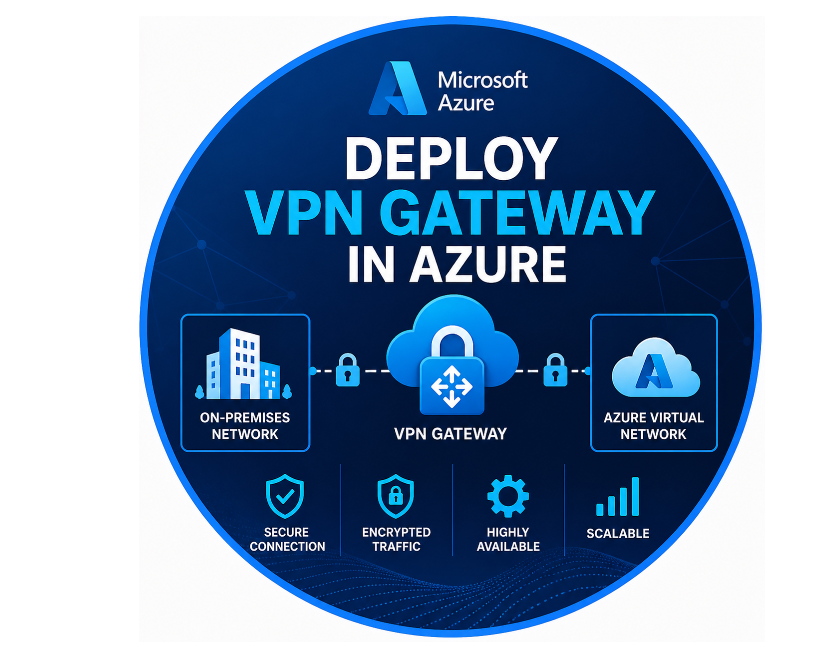
Setting up a secure Site-to-Site VPN between your on-premises WatchGuard Firebox T80 and Microsoft Azure is one of the best ways to connect your local network with Azure resources safely. In this step-by-step guide, I’ll walk you through the complete configuration process, including Azure setup, WatchGuard settings, routing, and troubleshooting common problems.
Before You Begin
To minimize future configuration changes on the Windows Azure site, plan your VPN architecture before you start. Think about these questions:
- Which site do you want to act as the hub for the VPN connection to the Windows Azure network? Because you can only configure a VPN tunnel from a single Firebox to Windows Azure, with a single VPN gateway, make sure that the Firebox you select has the capacity to handle the VPN tunnels you plan to configure, and that the Firebox has a highly reliable Internet connection. If you only plan to configure a VPN to one network, this is the site.
- How many networks do you want to connect? Do you plan to expand in the future? If you can plan ahead for how many subnets you might need, you can configure them once on the Windows Azure site, and not have to make changes later.
- Which subnets do you want to use for the VPN configuration? Plan carefully to avoid overlaps between the addresses at different remote sites.
As part of your plan, create a list of subnets for each device that you want to connect to the Windows Azure virtual network. Here is one example of a list:
| Network | Subnet |
|---|---|
| Azure site | 10.50.0.0/16 |
| Firebox Hub Trusted Firebox Hub Optional |
10.0.1.0/24 10.0.2.0/24 |
| Firebox B Trusted Firebox B Optional |
10.1.1.0/24 10.1.2.0/24 |
| Firebox C Trusted Firebox C Optional |
10.2.1.0/24 10.2.2.0/24 |
| Firebox D Trusted Firebox D Optional |
10.3.1.0/24 10.3.2.0/24 |
| Firebox D Trusted Firebox D Optional |
10.4.1.0/24 10.4.2.0/24 |
| Firebox E Trusted Firebox E Optional |
10.5.1.0/24 10.5.2.0/24 |
Configure the Windows Azure Virtual Network
To correctly configure your Windows Azure virtual network, read the Microsoft documentation. Microsoft recommends that you use an address space for the local network 10.1.0.0/16. For a tunnel switching configuration, select an address space that encompasses all of the subnets you plan to use for your connected Fireboxes. For example, the subnets 10.0.1.0/24, 10.15.1.0/24 and everything in between are within the subnet 10.0.0.0/12. If you want to create tunnel routes only for the specific subnets, you must add an additional address space entry for each subnet.
When you create the gateway, select Static Routing.
After you create the VPN gateway, follow the instructions below to gather the required information to configure the VPN connection on the hub Firebox.
Collect Gateway, Shared Key, and VPN Subnet Information
To establish a VPN connection from your local network to the Azure virtual network, you must gather certain pieces of information about the virtual network from the Windows Azure Management Portal. This configuration template has the information you must collect:
Prerequisites
Before you begin, make sure you have the following ready:
On Azure Side:
- An active Azure subscription
- A Virtual Network (VNet) already created
- A GatewaySubnet inside that VNet
- A Route-based VPN Gateway (IKEv2 supported)
On WatchGuard Side:
- WatchGuard Firebox T80 running Fireware OS version 12.x or newer
- A public IP address directly assigned to the Firebox
- Clear list of your on-premises LAN subnets
- No IP address overlap between your local network and Azure VNet
Information You Need to Collect
From Azure:
- Public IP address of the Azure VPN Gateway
- Azure VNet address space (CIDR)
- A strong shared secret (Pre-Shared Key)
From WatchGuard:
- Public IP address of your Firebox T80
- On-premises subnet(s) you want to connect
- Compatible IPsec proposals

Step 1: Azure Configuration
1.1 Create Local Network Gateway (LNG)
- Log in to the Azure Portal.
- Go to Local Network Gateways → Click + Create.
- Enter the following details:
- Name: lng-watchguard-t80 (or any name you prefer)
- IP Address: Public IP of your WatchGuard Firebox T80
- Address Space: Add all your on-premises subnets (example: 192.168.10.0/24)
- Click Review + Create and then Create.
1.2 Create the VPN Connection
- Go to your Virtual Network Gateway.
- Under Connections, click + Add.
- Configure these settings:
- Connection Type: Site-to-site (IPsec)
- Local Network Gateway: Select the one you just created
- Shared Key: Enter the same strong Pre-Shared Key (PSK) you will use on WatchGuard
- (Recommended) Click Customize to set IPsec/IKE policy:
- IKE Phase 1: AES256, SHA256, DH Group 14, Lifetime 28800 seconds
- IPsec Phase 2: AES256, SHA256, PFS Group 14, Lifetime 27000 seconds
Save the connection.
Step 2: WatchGuard Firebox Configuration
2.1 Create BOVPN Virtual Interface
- Log in to your WatchGuard Firebox Web UI.
- Go to VPN → BOVPN Virtual Interfaces → Add.
- Configure the following:
- Name: Azure-S2S
- Remote Gateway: Public IP of Azure VPN Gateway
- IKE Version: IKEv2
- Pre-Shared Key: Use the exact same key as in Azure
- Dead Peer Detection (DPD): Enabled (Traffic-based, Timeout 20s, Retries 5)
- NAT-T: Enabled with Keep-alive 20 seconds
2.2 Set IPsec Proposals
Match these settings with Azure:
Phase 1 (IKE):
- Encryption: AES256
- Integrity: SHA256
- DH Group: 14
- Lifetime: 28800 seconds
Phase 2 (IPsec):
- Encryption: AES256
- Integrity: SHA256
- PFS: 14
- Lifetime: 27000 seconds
2.3 Add Static Tunnel Routes
In the BOVPN Virtual Interface:
- Add the remote networks (Azure VNet CIDR) Example: 10.10.0.0/16
2.4 Create Firewall Policies
Create two firewall policies:
- From On-Premises to Azure
- From Azure to On-Premises
Important tips:
- Do not apply NAT on these policies
- Enable logging while testing
NAT Configuration Tips
To prevent one-way traffic issues, make sure:
- Traffic going from your local network to Azure is not NATed
- Always keep NAT disabled in the VPN-related firewall policies
Testing the VPN Tunnel
On Azure Side:
- Go to your VPN Gateway → Connections
- Check if the status shows Connected
- Monitor Bytes In and Bytes Out counters
On WatchGuard Side:
- Go to Dashboard → VPN Statistics
- The tunnel should show as Enabled and Established
- Check Traffic Monitor for successful Phase 1 and Phase 2 negotiations
Common Problems and Solutions
Problem 1: Tunnel is up but traffic flows only one way
Solution:
- Double-check that all on-prem subnets are added in Azure Local Network Gateway
- Verify there are no conflicting User Defined Routes (UDRs) in Azure
- Make sure NSG rules allow traffic to/from your on-prem subnets
- Confirm NAT is disabled on WatchGuard policies
Problem 2: Ping doesn’t work but VPN counters are increasing
Solution:
- The issue is usually the guest OS firewall on Azure VMs. Allow ICMP (ping) from your on-prem subnet.
Problem 3: Large packets are dropped
Solution:
- Enable MSS Clamping in WatchGuard Global Settings and set value between 1350–1360.
Recommended Settings Summary
Keep-Alive & DPD Settings:
- NAT-T Keep-Alive: 20 seconds
- DPD Mode: Traffic-based
- DPD Timeout: 20 seconds
- DPD Retries: 5
IPsec Proposals:
| Phase | Encryption | Integrity | DH/PFS | Lifetime |
|---|---|---|---|---|
| Phase 1 | AES256 | SHA256 | 14 | 28800 sec |
| Phase 2 | AES256 | SHA256 | 14 | 27000 sec |
This guide should help you successfully establish a stable Site-to-Site VPN between WatchGuard Firebox T80 and Azure.
If you face any specific error during setup, feel free to share the details in the comments and I’ll try to help.