Secure Business Networking with Site-to-Site VPN in 2026
Introduction to Site-to-Site VPN
In today’s connected business world, companies rarely operate from just one location. Head offices, branch offices, remote teams, and cloud resources all need to communicate securely. This is where Site-to-Site VPN becomes essential.
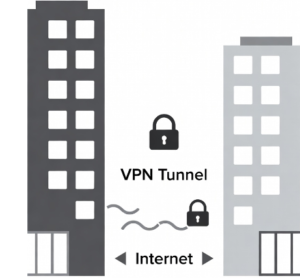
A Site-to-Site VPN, often abbreviated as S2S VPN, is a secure, encrypted connection that links two or more entire networks over the public internet. It allows computers, servers, and users in one physical location to access resources in another location as if they were all on the same local network.
Think of it like building a private, invisible tunnel between two offices. All data traveling through this tunnel is strongly encrypted, so even if someone intercepts it on the internet, they cannot read or use the information.
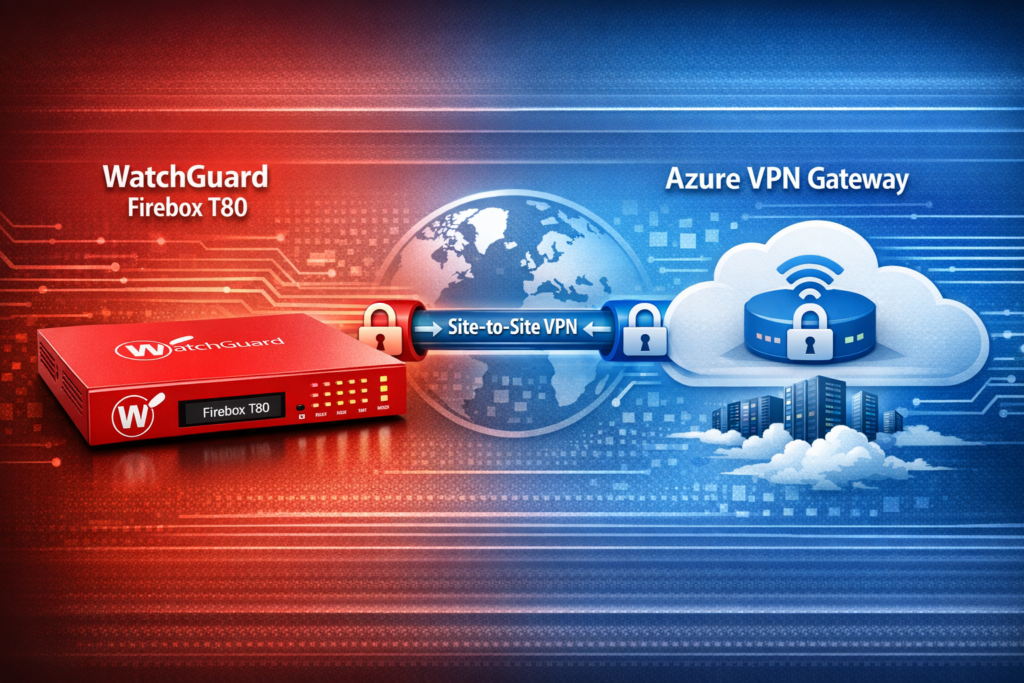
For example, if your main office is in Rawalpindi and you have a branch in Lahore or a cloud environment in Microsoft Azure, a Site-to-Site VPN lets employees in both places safely share files, access internal applications, printers, and databases without exposing sensitive data to the open internet.
Unlike the VPN you install on your laptop to browse securely (Point-to-Site VPN), Site-to-Site VPN connects entire office networks, making it the preferred choice for businesses of all sizes.
I’ve helped many small and medium businesses set up these connections, and in my experience, when done correctly, a Site-to-Site VPN is reliable, cost-effective, and highly secure.
Why Businesses Need Site-to-Site VPN
Modern companies use Site-to-Site VPN for many practical reasons:
- Securely connect multiple branch offices to headquarters
- Safely link on-premises networks with Microsoft Azure, AWS, or Google Cloud
- Reduce expensive dedicated leased lines (MPLS)
- Enable seamless file sharing and application access across locations
- Support hybrid work while keeping company data protected
- Improve business continuity and disaster recovery options
- Meet compliance requirements for data security
A well-designed Site-to-Site VPN can save thousands of dollars every year compared to traditional private connections while providing enterprise-level security.
Basic Types of Site-to-Site VPN
There are two fundamental types of Site-to-Site VPN technologies used today:
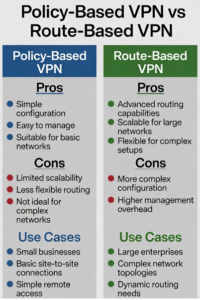
1. Policy-Based VPN
Policy-Based VPN is the traditional method. In this approach, you define specific rules or policies that tell the VPN device exactly which traffic should be encrypted and sent through the tunnel.
How it works: You create access lists that match source and destination IP addresses, and only matching traffic goes into the VPN tunnel.
Pros:
- Simple to understand for small setups
- Straightforward configuration on many older devices
Cons:
- Less flexible as the network grows
- Difficult to manage complex routing scenarios
- Not ideal when using dynamic routing protocols
This type was very popular 10–15 years ago but is now less common for new deployments.
2. Route-Based VPN
Route-Based VPN is the modern and preferred method. Instead of using strict policies, it creates a virtual tunnel interface (VTI). You then add normal routes (static or dynamic) to direct traffic into that tunnel.
How it works: The VPN tunnel behaves like a normal network interface. Routing decisions determine what traffic goes through the tunnel.
Pros:
- Highly flexible and scalable
- Supports dynamic routing protocols (BGP, OSPF)
- Much easier to troubleshoot
- Better performance with large or complex networks
- Natively supported by cloud providers like Azure
Cons:
- Slightly more initial configuration on some devices
Which type is more important and mostly used today?
In 2026, Route-Based VPN is by far the most popular and important type. The majority of new Site-to-Site VPN deployments — whether between firewalls like WatchGuard Firebox, Cisco, FortiGate, or connecting to Microsoft Azure — use Route-Based VPN.
It has become the industry standard because it is easier to manage, scales better, and works seamlessly with cloud environments. Most experts strongly recommend Route-Based VPN for any new setup.
Benefits of Using Route-Based Site-to-Site VPN
- Easier addition of new subnets or remote sites
- Better support for redundant connections and failover
- Improved compatibility with cloud VPN gateways
- Simpler troubleshooting with standard routing tools
- Future-proof for growing networks
Real-World Use Cases of Site-to-Site VPN
- Multi-Branch Companies — Head office connected to 5–10 branch locations.
- Hybrid Cloud — On-premises network securely connected to Azure or AWS.
- Partner Networks — Secure connection between two different companies.
- Disaster Recovery — Backup site always ready with live replication.
- Retail Chains — Central inventory system accessible from every store.
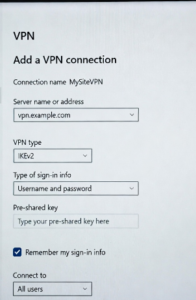
How to Configure Site-to-Site VPN on a User PC (Windows)
Important Note: A true Site-to-Site VPN is configured between two network devices (firewalls or cloud gateways). However, if your company provides VPN gateway details, you can connect your individual Windows PC to the remote network.
Here is a detailed, step-by-step guide to set up the connection on Windows 11 / Windows 10:
- Click the Start button and open Settings.
- Go to Network & Internet → Select VPN from the left menu.
- Click Add VPN connection.
- Fill in the following details carefully:
- VPN provider: Windows (built-in)
- Connection name: Something clear like “Company Head Office VPN”
- Server name or address: Enter the public IP address or hostname of the remote VPN gateway (provided by your IT admin)
- VPN type: Select IKEv2 (recommended for best security and stability)
- Type of sign-in info: Choose Pre-shared key (most common) or User name and password
- Enter the Pre-Shared Key or credentials given by your administrator.
- Click Save.
- Back on the VPN list, select your new connection and click Connect.
Once connected, your PC will behave as if it is inside the remote office network. You can then access shared folders, internal websites, or remote desktop sessions.
Troubleshooting Tips for PC Connection:
- If it fails to connect, double-check the server address and Pre-Shared Key.
- Try changing VPN type to L2TP/IPsec if IKEv2 doesn’t work.
- Make sure your Windows firewall is not blocking the connection.
Update Windows to the latest version.
Full Site-to-Site VPN Configuration Best Practices
When setting up a professional Site-to-Site VPN between two locations or with Azure, always follow these best practices:
- Use Route-Based configuration on both sides
- Choose strong encryption: AES-256 + SHA-256
- Use IKEv2 protocol whenever possible
- Create unique, long Pre-Shared Keys and change them periodically
- Enable Dead Peer Detection (DPD) with reasonable timeout values
- Avoid IP address overlap between the two networks
- Document all subnets and routing information
- Test thoroughly with ping, file transfer, and application access
- Enable logging on both firewalls for future troubleshooting
- Consider implementing redundancy with two VPN tunnels
Common Challenges and How to Overcome Them
- Tunnel establishes but no traffic flows → Usually a routing or firewall policy issue. Check that all required subnets are added on both sides.
- One-way traffic only → Verify routing tables and NAT settings. Disable NAT on VPN traffic.
- Frequent disconnects → Adjust DPD and NAT-T keep-alive settings.
- Large file transfers fail → Enable MSS clamping (usually 1350–1360).
- Azure connection issues → Make sure all on-prem subnets are added to the Local Network Gateway in Azure.
With careful planning and testing, most of these issues can be avoided.
Security Considerations for Site-to-Site VPN
- Always keep firewall firmware and VPN software updated
- Use strong authentication methods
- Implement least-privilege access policies
- Monitor VPN logs regularly for suspicious activity
- Consider adding multi-factor authentication where possible
- Regularly audit connected subnets and users
Future of Site-to-Site VPN
Even with the rise of SD-WAN and Zero Trust solutions, Site-to-Site VPN remains a core technology for secure connectivity. Modern implementations are becoming smarter with automated failover, better performance, and tighter integration with cloud platforms.
Conclusion
Site-to-Site VPN is a proven, secure, and cost-effective way to connect multiple locations and cloud resources. While Policy-Based VPN still exists, Route-Based VPN is the clear winner in 2026 due to its flexibility, scalability, and ease of management.
Whether you are connecting two offices or linking your local network with Microsoft Azure using a WatchGuard Firebox, understanding the basics and following proper configuration steps will give you a stable and secure connection for years to come.
If you are planning to set up a Site-to-Site VPN, start with Route-Based configuration and test thoroughly. Feel free to share your specific setup (WatchGuard, Azure, Cisco, etc.) in the comments, and I’ll be happy to provide more targeted advice.
Stay safe, keep your connections secure, and happy networking!